CloudOps is often asked to provide proposals for organizations migrating to cloud IaaS from their local or self-managed physical servers by people very experienced with virtualization, SANs and dedicated servers. Questions frequently come up about what level of RAID we use in cloud storage and how long it takes to increase the storage amount available to a server. There is also concern with using network storage, as it is perceived to be slower.
cloud.ca Demo at Citrix Synergy
cloud.ca is a Citrix Ready verified regional IaaS, meaning that it is trusted to enhance Citrix solutions for cloud infrastructure and end-user compute workloads. As such, we were invited to demo our platform at Citrix Synergy a couple of weeks ago in Orlando, FL.
cloud.ca Goes to Citrix Synergy
Earlier this month a CloudOps team attended Citrix Synergy in Orlando, FL. For those of you who aren't familiar with it, it's a three day event for Citrix partners and customers focused on enterprise mobility, not to mention a great place to network and have a bit of fun.
Cloud IaaS vs Host Virtualization
Previously, I blogged about differences between hosting and cloud on cloudops.com. To continue with the theme of contrasting Infrastructure as a Service (IaaS) cloud to things that are often confused with cloud, in this post I will compare IaaS cloud to virtualization. First off, SaaS can run on cloud, but is not cloud. I am strictly referring to an IaaS cloud.
Different people have different security needs, but everybody agrees that having more security options is a good thing. Two-factor authentication (2FA), also called two-step verification, is one such option that is becoming more prevalent these days. Its purpose is simple: add an extra layer of security to the login process of your application (in our case, cloud.ca’s web console).
Three Ways Cloud Will Reduce Your CFO’s Stress
Getting IT wrong is stressful. Cost savings are leading CFOs to consider moving to the public cloud, but the real value of cloud comes from the business agility it enables.
Peerio Uses cloud.ca, Canada's cloud infrastructure as Part of Its Multi-cloud Strategy
Peerio integrates cloud storage with a messaging platform so users can safely keep their important files online and ready to send from anywhere. With end-to-end encryption, messages and files are encrypted before leaving the client’s computer and can only be read by senders and recipients.
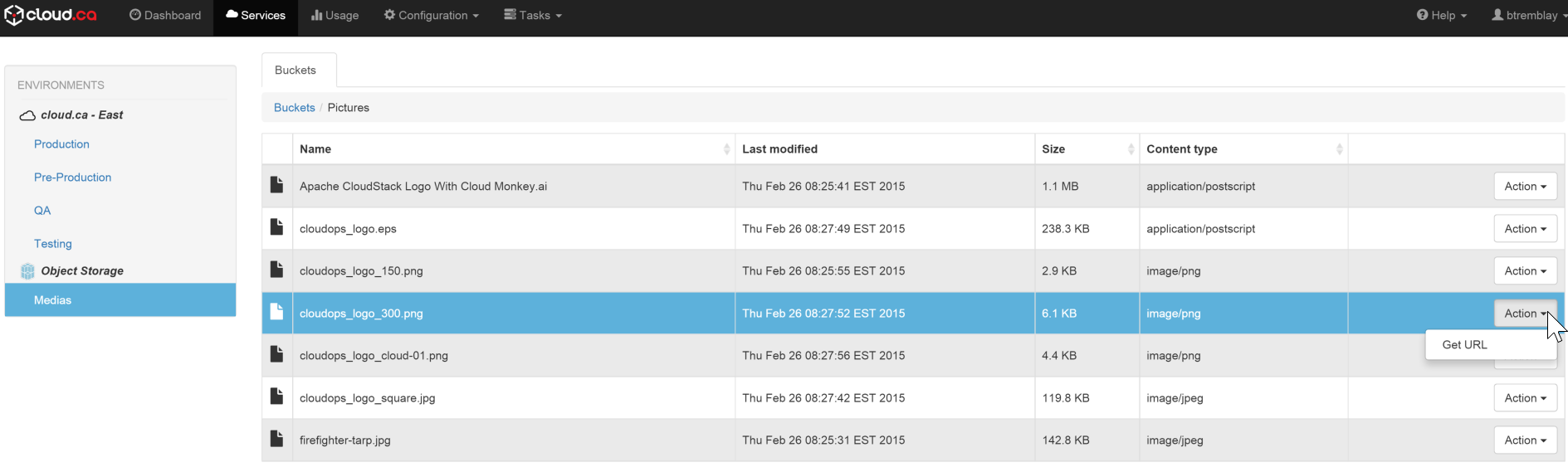
cloud.ca Object Storage; An Efficient and User-friendly Web Interface
A well designed object storage platform provides developers with an efficient way to access, store, protect and distribute their digital content independently.
New Architectures in a Cloudy World
Cloud computing is a victim of its own success. For one thing, cloud advocates have promised so much—worry-free, turnkey IT that just works— that the reality is bound to disappoint. Worse, clouds seem immune to tough economic times, so nearly every technology company is wrapping itself in a cloud mantle, and every dynamic website is claiming it’s a cloud. We don’t want to get bogged down in definitions, but any discussion of clouds requires a clear understanding of three things: